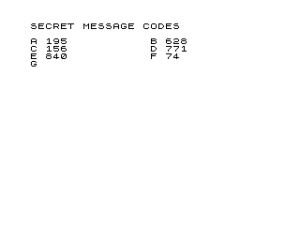
This program generates a simple substitution cipher reference table by assigning a unique random three-digit number (0–999) to each letter of the alphabet. It uses a collision-detection loop (lines 42–44) to guarantee that no two letters share the same code, resampling whenever a duplicate is found. The results are printed as letter–number pairs across the screen using the comma-column layout.
Program Analysis
Program Structure
The program is short and linear, falling into three logical phases:
- Initialisation (lines 5–25): prints a title, seeds the random number generator with
RAND, sets up the alphabet stringA$, and dimensions a 26-element numeric arrayA()to record used codes. - Code generation and display (lines 30–65): a
FOR N=1 TO 26loop picks a random integer 0–999 for each letter, checks it against all previously assigned codes, and prints the letter–code pair. - Save / restart (lines 70–80): saves the program and provides a
RUNline to regenerate a fresh table.
Random Code Generation
INT (1000*RND) at line 40 produces an integer in the range 0–999, giving 1000 possible codes for 26 letters — a comfortable surplus that keeps the collision rate low. The inner loop at lines 42–44 walks the entire A() array; if the candidate C matches any previously stored value, execution jumps back to line 40 to resample. Because DIM A(26) zero-initialises the array, the value 0 is a valid code that could collide with an uninitialised slot on the very first iteration — a minor edge-case anomaly. In practice the probability is negligible (1 in 1000), but a strict implementation would initialise used-code slots to a sentinel outside the 0–999 range.
Key BASIC Idioms
- Alphabet string indexing:
A$(N)selects the Nth character ofA$, a standard ZX81/TS1000 single-character substring idiom. - Comma column layout: the trailing comma in the
PRINTstatement at line 50 uses the 32-column tab-stop mechanism to arrange letter–code pairs in two columns across the screen. - RAND with no argument: line 10 uses bare
RANDto seed from the frame counter, ensuring a different table each run. - Triple comma spacing: line 6 uses
,,,after the title string to advance three tab columns, creating visual separation before the data.
Notable Techniques
The collision-avoidance strategy is a simple linear scan rather than a shuffle (e.g. a Fisher-Yates approach). For only 26 elements this is perfectly adequate; worst-case behaviour is bounded because the pool of 1000 codes vastly outnumbers the 26 required slots. The technique does mean the inner loop at lines 42–44 runs up to 26 iterations per letter, for a total of up to 351 comparisons — negligible on any hardware running this code.
Bugs and Anomalies
| Line | Issue | Impact |
|---|---|---|
40–43 | DIM A(26) initialises all elements to 0; the code 0 can therefore falsely collide with an unused slot during generation of the very first letter. | Extremely rare (0.1% chance) but could cause an unnecessary extra RND call for the first letter only. |
70 | SAVE "1003%6" — the %6 escape encodes an inverse-video digit, acting as an auto-run flag embedded in the filename. | Cosmetic / intentional; causes the program to run automatically when loaded. |
Content
Source Code
5 REM SECRET MESSAGE 1
6 PRINT "SECRET MESSAGE CODES",,,
10 RAND
20 LET A$="ABCDEFGHIJKLMNOPQRSTUVWXYZ"
25 DIM A(26)
30 FOR N=1 TO 26
40 LET C=INT (1000*RND)
42 FOR X=1 TO 26
43 IF C=A(X) THEN GOTO 40
44 NEXT X
45 LET A(N)=C
50 PRINT A$(N);" ";C,
60 NEXT N
65 STOP
70 SAVE "1003%6"
80 RUN Note: Type-in program listings on this website use ZMAKEBAS notation for graphics characters.